Angelo State University partnered with Groove Jones to create immersive digital experiences for the ASU Mobile STEM Innovation Lab, an initiative designed to bring hands-on STEM education to students across West Texas. The goal was to translate complex subjects like cybersecurity into engaging, interactive experiences that spark curiosity and make learning tangible for middle and high school students.

As part of this initiative, Groove Jones developed the Cybersecurity Command Center VR experience, an action-driven simulation that places students inside a high-stakes digital defense scenario.

The Experience
Students are recruited into the Angelo State Cyber Security Defense Force and immediately alerted to an incoming threat. Their objective is clear: protect the mainframe, secure sensitive data, and prevent system breaches.

Designed as an interactive simulation, the experience transforms abstract cybersecurity concepts into fast-paced, tangible challenges. Instead of passively learning terminology, students actively defend a virtual system by deploying antivirus software towers, activating firewalls, and eliminating malicious threats as they appear.

Each level is designed to introduce students to a different concept in cybersecurity. Each wave represents a specific type of threat, while also introducing new tools to combat it. Most threats can be handled using firewalls and antivirus software, while phishing attacks are best addressed with email filtering systems. More advanced threats require stronger defenses like encryption or two-factor authentication to fully secure the system.

Players must apply this knowledge in real time, strategically building a network of defensive structures to protect their mainframe and keep it online. Inspired by tower defense gameplay, the experience requires students to think critically, adapt quickly, and build layered security systems that evolve with each wave.
A Tower Defense-Inspired VR Game with Learning Progression
The experience unfolds across eight escalating waves of cyber threats, each designed to introduce a specific concept and corresponding defense strategy. At the end of each wave, students complete a short knowledge check to reinforce what they’ve learned.
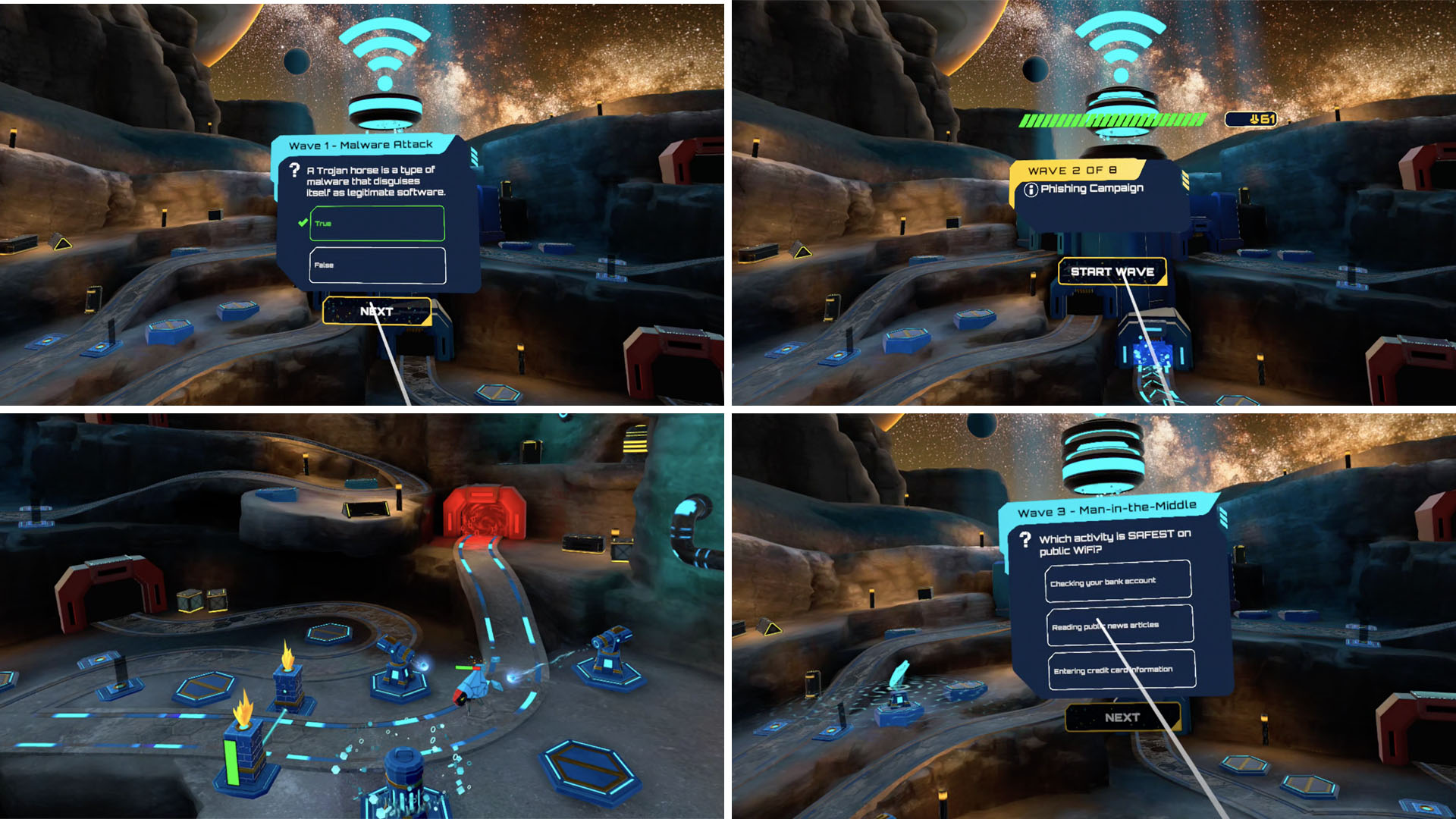
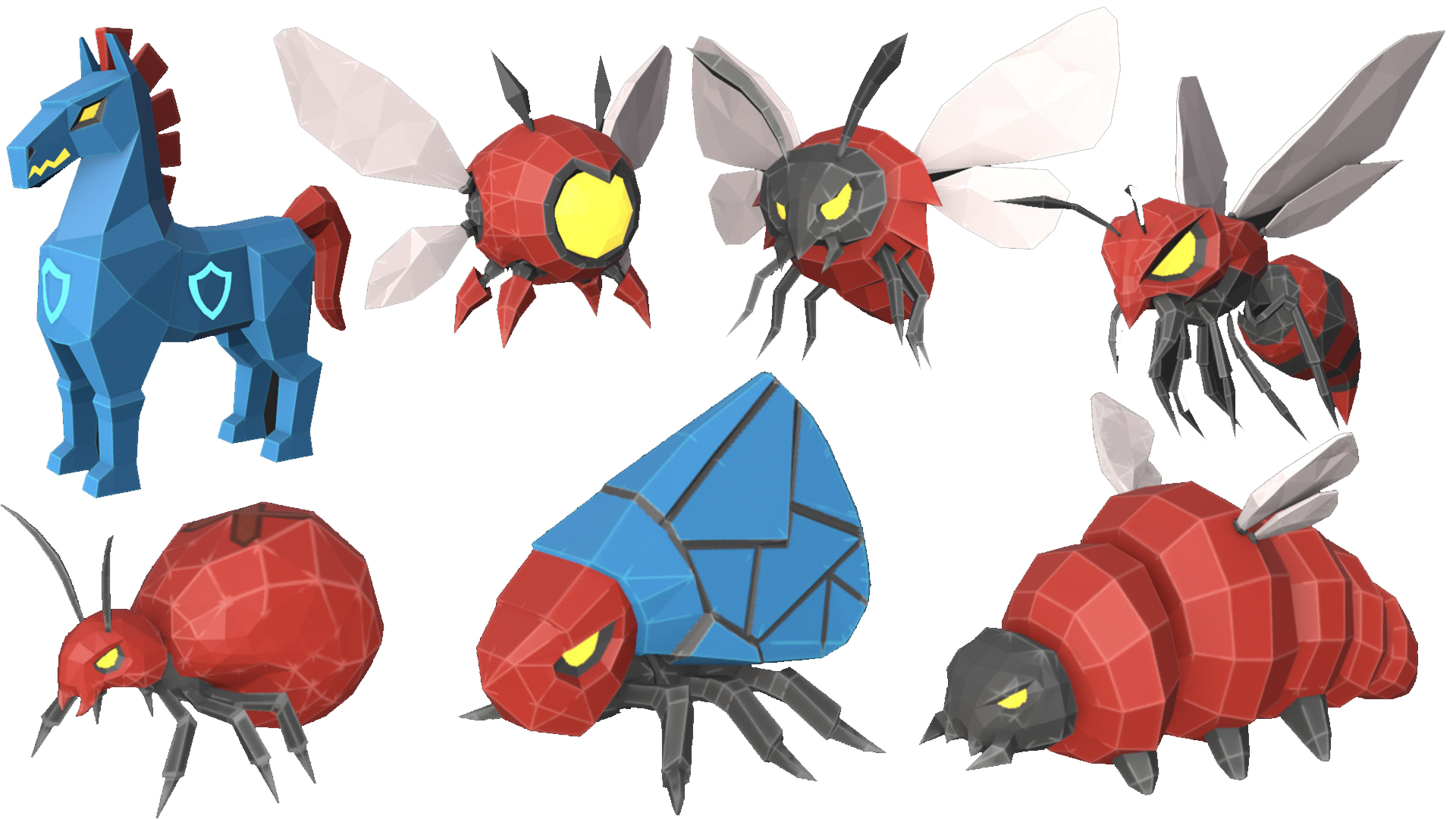
Wave One: Malware, Adware, and Trojans

Wave Two: Phishing Attacks
This wave introduces the Filter Tower, designed to “filter out” malicious emails. Phishing threats appear as deceptive messages attempting to access sensitive data. Students learn to identify red flags while defending their system, followed by a knowledge check to reinforce key concepts.

Wave Three: VPN Security and Encryption
Students are introduced to secure network concepts and data protection. The Encryption Software Tower reveals hidden enemies, including a “Man-in-the-Middle” attacker represented through a mustache and sunglasses disguise. This visual metaphor helps explain how attackers intercept data on public networks and how VPNs protect against these vulnerabilities.
Wave Four: Password Attacks and Authentication
This wave focuses on brute force and credential-based attacks. Students unlock an extra layer of defense, representing a password tower, and can upgrade existing defenses like firewalls. Enemies include advanced script-based attackers, emphasizing the importance of strong authentication practices and layered security.

Wave Five: Distributed Denial of Service (DDoS)
Players gain the ability to upgrade most towers to Level 2, increasing range, speed, and effectiveness. The DDoS threat appears as swarms of small enemies that overwhelm the system collectively, teaching students how volume-based attacks can disrupt infrastructure.

Wave Six: Zero-Day Exploits and Advanced Tools
This wave introduces consumable tools like Honeypots and Patch systems, allowing players to slow or eliminate large groups of enemies. The Zero-Day Exploit threat appears as a hidden worm that remains undetected until revealed, reinforcing the concept of unknown vulnerabilities.

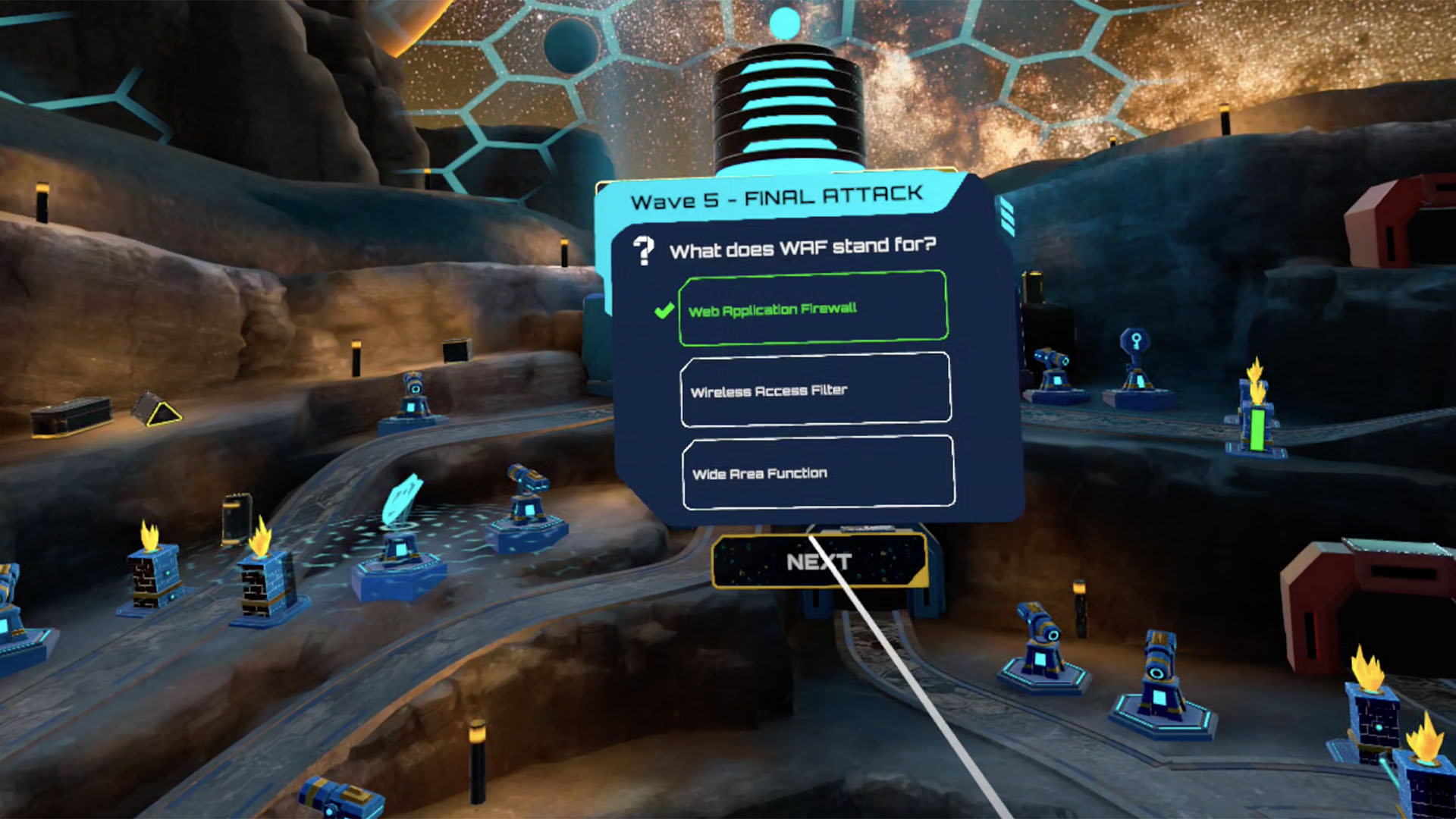
Wave Seven: Web Application Firewall (WAF)
Students learn about advanced perimeter defenses as the environment becomes shielded by a digital dome. The SQL Injection threat poses a powerful, high-impact adversary, highlighting the risks of database vulnerabilities and the need for specialized protection.
Wave Eight: Full System Attack
The final wave combines all previously introduced threats into a single, high-intensity scenario. Students must apply everything they’ve learned to defend the system, testing their ability to think strategically under pressure.
Throughout the experience, enemies are designed as visual representations of their real-world counterparts, from phishing emails resembling insect-like creatures to disguised attackers revealed through encryption. This approach makes invisible digital threats tangible and easier to understand.
At the end of the game experience, students are given a score rating via a “Performance Report.”

They also unlock a STEM Career, which is based on actual careers in the field of cybersecurity in the San Angelo area, which includes a breakdown of education required based on ASU classes, and a career path for the individual.

Core Learning Outcomes
Students develop practical knowledge by:
- Identifying and responding to cyber threats
- Understanding layered security strategies
- Applying critical thinking in real-time scenarios
- Recognizing how different attack types impact systems
- Learning how cybersecurity professionals defend digital infrastructure
The combination of gameplay, repetition, and escalating difficulty reinforces both engagement and retention.

Conclusion
The Cybersecurity Command Center VR experience transforms a complex and often abstract subject into an engaging, interactive learning environment. By placing students directly inside a simulated cyber attack, the experience bridges the gap between theory and real-world application.

Groove Jones helped Angelo State University create a powerful educational tool that builds both understanding and confidence. Students leave the experience not only with foundational cybersecurity knowledge but with a clearer sense of how these skills apply in real-world careers, making the field more accessible, relevant, and exciting.




